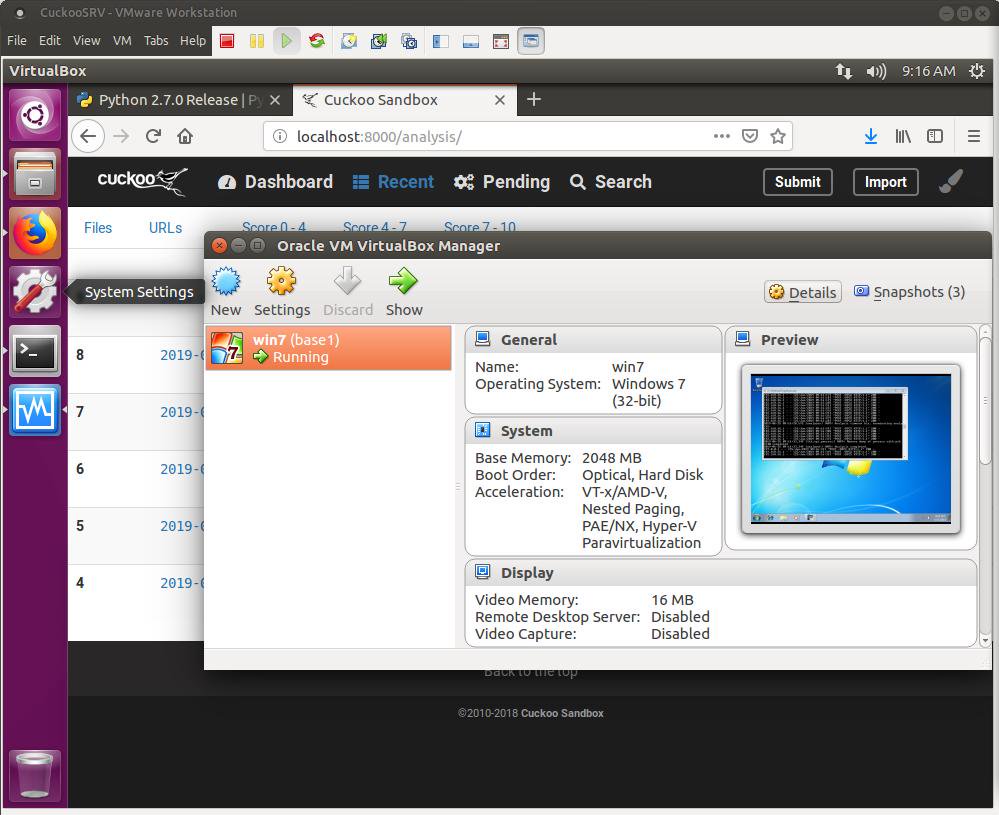
This post should cover the basics of how to import and run a basic analysis using the Cuckoo VM which could be found here. I’m referring to this VM as CuckooVM version 2, since if you’ve been following, you already know that I have shared a previous version of this CuckooVM which I configured. Even if you do not do malware analysis or digital forensics and incident response, this VM could come handy and useful to you, so please do not skip just because you’re not working in those areas.
Now, in order to use the Cuckoo Sandbox which I think many of the online service providers today have their systems built around Cuckoo (no proof to this claim!), you will need a dedicated machine. The installation process itself is also not simple for some, but it could be a piece of cake to others (not saying it is for me!), so this VM could save you the trouble of:
1. Need to purchase or dedicate a whole machine for Cuckoo (it is worth though!)
2. Need to go through the installation process
Before moving forward, if any of the figures below is not clear, just click on it to enlarge it.
INTRODUCTION
The Cuckoo VM is running Cuckoo in what is called a “Nested Virtualization”. What that means, well first let’s check this general architecture as seen in figure 1.1.
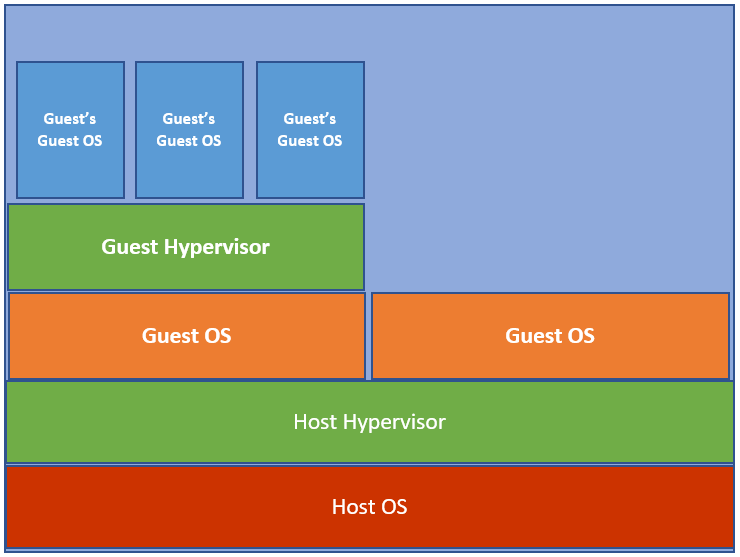
Figure 1.1 – General Architecture
Continue reading